Wireless networking is convenient, fast, and provides a lot of computing mobility. Wifi does, however, require extra measures if it is to be as secure as hard-wired networks. And WPA is the standard to use.
SURVEILLANCE OF WIRELESS NETWORKS
Consider for a moment the number of wireless networks visible to a laptop in a good wifi location. There is probably a small number of strong signals, and a larger number of fair signals, and a large number of weak (but readable)signals. Anyone with software and hardware capable of monitoring the airwaves can capture wireless data and subject it to analysis. In some ways, WiFi is similar to the telephone party lines of long ago, when it was possible to simply listen and gather information on the other people with access to the line. Woe unto the person giving up sensitive data over such a channel. It really is an important matter considering the "long tail" population of fair to weak networks that are perhaps too weak for connections, but still strong enough to tap from far away!
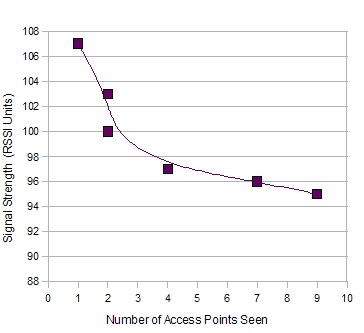
Plenty of weak 802.11 signals are yet
strong enough for surveillance!
Unsecured wireless networking should be used only for things that are okay for the public to see. For all other data, encryption is necessary.
For a long time, the popular solution to keeping wireless network data safe from prying eyes was Wired Equivalent Privacy (WEP). It provided a means of securing communications in the age of intel 486 processors, but now it is quite ineffective. If your network is still using WEP, you are as vulnerable to surveillance as if you used no encryption. Stop using WEP and switch to WPA.
WEP's weakness is in its tendency to leak data about the encryption key, which can be used to break the key in a matter of minutes. In essence, the attacker captures all traffic on the network, then applies a statistical algorithm to determine the key. When the key is broken, the attacker may use the network infrastructure and has access to its data. One can then monitor all users' surfing habits, collect passwords, et cetera.
The safer encryption protocol is WiFi Protected Access (WPA). It uses a more secure scheme for managing keys, and is orders of magnitude more resistant to cryptanalysis. One essential requirement with WPA is to select a password that is NOT composed of known words that can be found in a dictionary, as there have been demonstrations of WPA keys being "reverse engineered" to poor key selection by end users. It is that password which, along with the network SSID, used as seed to produce one very long and tough wireless crypto key. Attackers essentially pre-compute keys (once) using common SSIDs and dictionary words, and build "rainbow tables" to simply look up the keys (any number of times).
COUNTERMEASURES AGAINST WIRELESS NETWORK SURVEILLANCE
No cryptosystem is totally secure; the best simply take more time and resources to break than the attackers are willing to sacrafice. The smartest policy is to keep sensitive data off the network, and use WPA if the network must be used for semi-sensitive data. For more reading on the recent advances in cryptanalysis of WPA, see Practical attacks against WEP and WPA by Beck and Tews.
Sometimes there simply isn't a secure wireless network available. In addition, very sensitive data should always be hidden from wireless hackers, dictatorial authorities, and institutions disrespecting individual privacy. Excellent data security is available in the form of Virtual Private Networking (VPN). VPN is a service that protects data by creating an encrypted channel between the user's computer and a trusted server in a distant location. The distant server is the connection point to the internet, and the user's IP address reflects that trusted server's location. Using a VPN makes it impossible for an institution or government to restrict a user's internet access, sniff sesitive data, or track a user's browsing. VPN can also provide anonymity superior to that offered by popular web based proxy services. It is important to realize that a VPN acts as a "secure nettork interface" and protects the flow of all data in and out of the computer - not merely web browser activity. FTP, VOIP, and other non-browser data are protected.
Whether you are a telecommuter working from home, a journalist writing an expose on your government's misuse of power, or simply a person doing online banking, consider protecting yourself and your work by using WPA for wireless and VPN for all networking.
© 2005 - 2024 AB9IL.net, All Rights Reserved.
About Philip Collier / AB9IL, Commentaries and Op-Eds, Contact, Privacy Policy and Affiliate Disclosure, XML Sitemap.
This website is reader-supported. As an Amazon affiliate, I earn from qualifying purchases.